Compare with 1 courses
Ethical Hacking
₹ 549
₹ 599
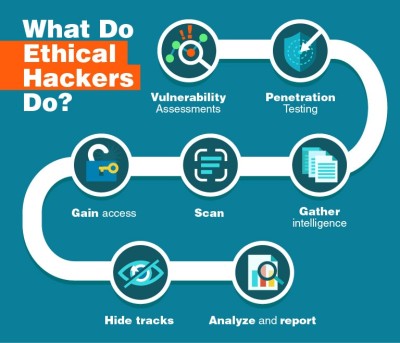
This course provides a comprehensive introduction to ethical hacking, covering the methodologies, tools, and techniques used by security professionals to identify and mitigate vulnerabilities in computer systems and networks. Participants will learn how to conduct ethical hacking assessments, understand common attack vectors, and apply defensive strategies to enhance cybersecurity posture.
Learn more
 0
0 